DevOps
Enable MongoDB Remote Connections Safely: bindIp, mongod.conf, and Firewall Basics
MongoDB ships bound to localhost for a reason. When you truly need another host on the wire, coordinate net.bindIp in mongod.conf, systemd restarts, and firewall intent the same way you would for Redis or Postgres on the same VPS.
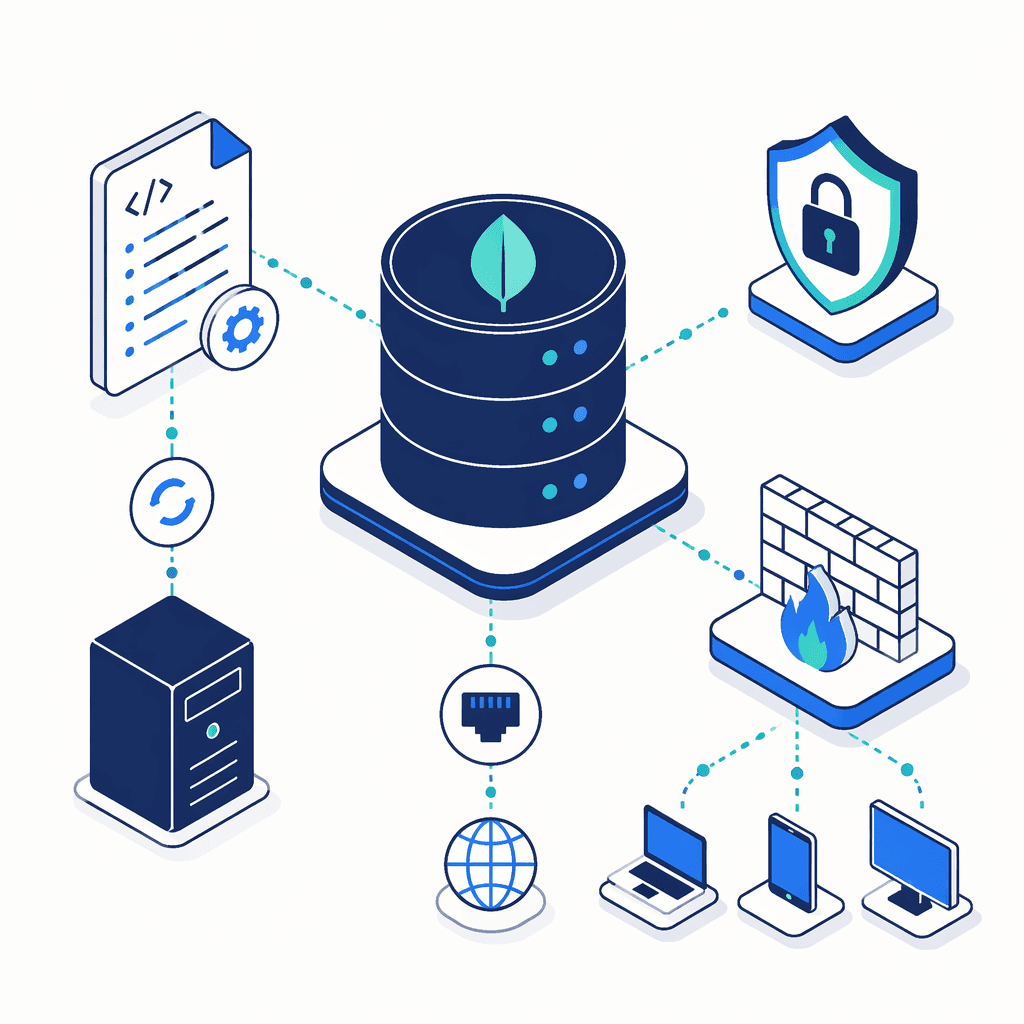
MongoDB listens on 127.0.0.1 by default because that keeps casual network scans away from 27017. When apps on another VM or your laptop genuinely need native drivers instead of tunnels, tighten net.bindIp, restart mongod, confirm the listener, then think about firewall allow lists and SCRAM passwords. Pair this with MongoDB 7 on Ubuntu when the binaries are brand new—the networking story here assumes mongod.conf already exists.
⏱️ Estimated hands-on time: ~10 minutes
Why exposing database ports is never “just firewall later”
Opening TCP 27017 to the WAN is workable in labs and dangerous in prod. Prefer VPNs, bastion SSH tunnels, cloud security groups, or IP allow lists; require TLS-capable deployments where policy demands it; and never rely on anonymity—bots enumerate MongoDB listeners for sport.
Prerequisites and risk checklist
Before editing anything, line up:
- MongoDB installed (
mongod.servicerecognizable to systemd) and runnable with sudo/root - The server’s own IPs — private VPC address, public elastIP, whichever NIC your clients target
- A rollback plan (config backup) because YAML mistakes brick the daemon silently
When you inevitably touch UFW on the host, I still paste sequencing from the Nginx + UFW command slab so ufw status verbose rhythms stay identical beside database work.
Remote reachability piles risk: strong credentials, patched builds, outbound monitoring, least-privilege MongoDB roles. If Postgres on the neighboring VM already hardened listeners, skim PostgreSQL remote access for the analogous pg_hba.conf mindset—different files, identical paranoia.
Configure bindIp in mongod.conf
- Open the YAML config (Ubuntu/deb layouts keep it at
/etc/mongod.conf):
sudo nano /etc/mongod.conf
- Find the
net:block. Stock installs pin everything to localhost:
net:
port: 27017
bindIp: 127.0.0.1
127.0.0.1 means only shell traffic on that machine may connect—exactly why remote tooling times out immediately.
- Append the server NIC(s) Mongo clients dial, preserving loopback:
net:
port: 27017
bindIp: 127.0.0.1,10.10.14.88
10.10.14.88 is illustrative—swap your interface address. Omit spaces after commas; YAML sees spaces as separators for additional tokens and mongod may refuse to boot.
Reach-every-interface mode (bindIp: 0.0.0.0) listens widely and belongs only behind ironclad network controls—mirror the playbook from the firewall section before you even consider it.
Reload mongod cleanly
- Save (Ctrl + O, Enter) and exit (Ctrl + X in nano).
- Restart the unit so networking reloads:
sudo systemctl restart mongod
- Optional sanity: confirm systemd accepted the job without instant failure:
sudo systemctl status mongod --no-pager
If Active: failed flashes, jump to logs before touching clients.
Verify status and MongoDB logs
systemctl status already hints at exit codes, but MongoDB’s own log tells you whether bind succeeded:
sudo tail -n 60 /var/log/mongodb/mongod.log
Look for “Listening on” lines that include the addresses you expect. Absent that, the daemon never opened the socket—no amount of driver retries fixes silent bind failures.
Troubleshooting connection failures
Work through the boring stack first—most “remote access” tickets die here:
mongodactually running?systemctl is-active mongod- Syntax in
/etc/mongod.conf—YAML indentation undernet:still matters when nested keys grow - Correct IP in bindIp (server-facing, routable from the client subnet)
- Host firewall vs. cloud SG: open TCP 27017 only for known peers. When I need the exact
ufw allow/ufw status verbosecadence without retyping, that nginx-focused snippet already documents the muscle memory. - Corporate Wi-Fi or CGNAT paths intercepting outbound DB traffic—test from a bastion inside the VPC if possible
Firewall and authentication layering
- UFW / iptables / security groups — allow the minimum sender IPs just like you would after the paste-friendly Ubuntu firewall steps on web-tier boxes.
- SCRAM users — create least-privilege database users before you treat wide bind as “done.”
- TLS — wire net.tls when clients cannot live inside a VPN.
- Patch cadence — mongod CVEs land regularly; snapshot backups before major upgrades.
- Logging & auditing — tail slow queries and auth failures once strangers can route to the port.
Frequently asked questions
Should I bind MongoDB to 0.0.0.0?
Only when every interface must listen and independent controls (firewall + auth + segmentation) already shrink the blast radius. Most Ubuntu VPS installs stay calmer when 127.0.0.1 plus each real NIC IP is explicit—0.0.0.0 is a blunt instrument that saves typing and costs sleep.
Which IP address goes in bindIp?
List the MongoDB machine’s listener addresses—the loopback plus each routable NIC your clients hit—never the analyst laptop trying mongo mongodb://.... Keep comma-separated tokens tight; stray spaces become surprise tokens.
Does widening remote connectivity require MongoDB authentication?
No automatic enforcement ships with bindIp edits. Packet routing and credential checking are different subsystems: tighten bindIp, then ensure SCRAM (or x.509) users exist before anything production-adjacent touches the port.
Why would bindIp look correct yet drivers still hang?
Validate systemd actually reached active (running), inspect /var/log/mongodb/mongod.log for bind errors, confirm UFW and cloud groups both allow the same CIDR, and only then chase URI strings or driver versions.
You now know how to extend bindIp, restart mongod, read the proof in logs, and stack firewall plus auth without treating reachability as safety. Exercise the flow in staging, compare notes with Install MongoDB 7 on Ubuntu Server if packages need alignment, and keep the nginx + UFW snippet beside this tab whenever firewall edits land next to database work.
Written by Shashikant Dwivedi
Engineer, occasional writer, full-time noticer. Based in Prayagraj, India. New essays land roughly twice a month.
Keep reading
Adjacent essays.
The newsletter
New articles in your inbox.
Occasional articles on engineering, tooling, and software development practices. No marketing, no fluff — just the article, when it's ready.
Unsubscribe with one click. Your email never leaves the list.